AGF — Agentic Governance Framework
A reference architecture for governed agentic systems — synthesizing NIST, OWASP, CSA, ISO, EU AI Act, OpenTelemetry, MITRE ATLAS, and academic research into a composable governance framework.
The Problem
The governance landscape for agentic AI is fragmented. NIST provides risk management frameworks. OWASP provides threat taxonomies. CSA provides trust frameworks. ISO provides management systems. OpenTelemetry provides observability standards. The EU AI Act provides regulatory requirements. Every one of these institutions is doing critical work — but the pieces haven’t been assembled into a single coherent architecture that practitioners can follow.
AGF is an attempt to sort those pieces and show how they fit together. We didn’t invent these patterns. We connected existing work — from distributed systems, security engineering, compliance, and control theory — and named them for the agentic context.
Read the full framework at agf.jessepike.dev →
The Rings Model
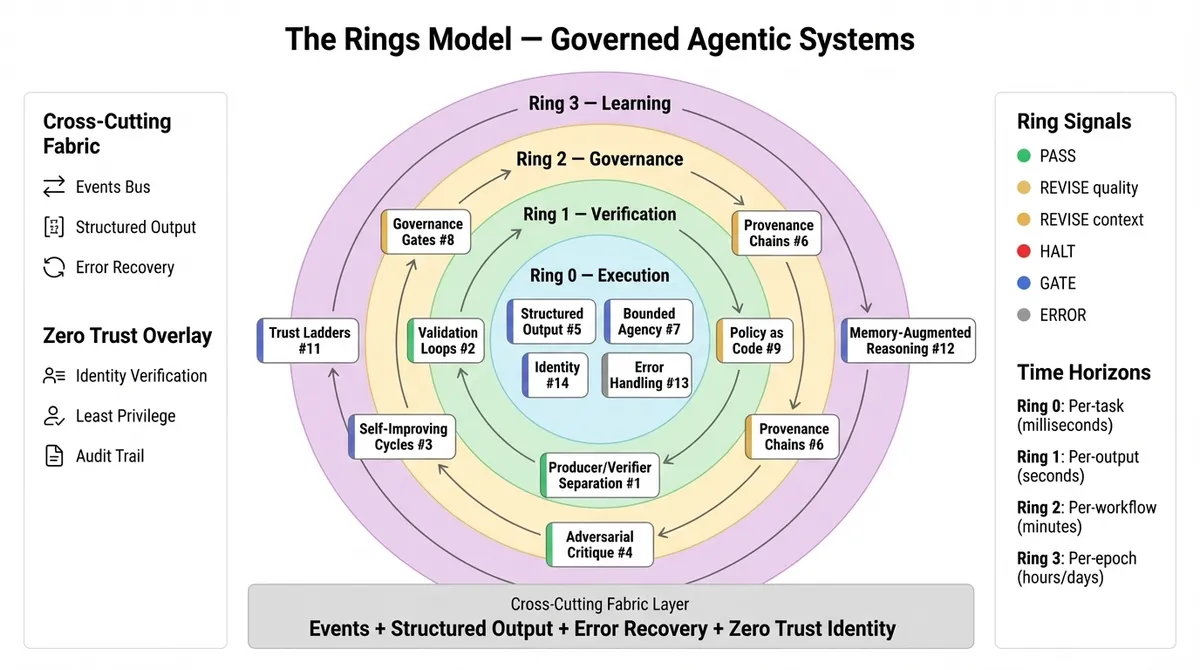
Four concentric rings organize governance into composable layers:
| Ring | Function | Principle |
|---|---|---|
| Ring 0 — Execution | The agent performs its domain task | Do the work |
| Ring 1 — Verification | A separate process validates the output | The agent that creates must not be the sole agent that validates |
| Ring 2 — Governance | Policy evaluation, human gates, authorization | Decisions with material impact require governed approval |
| Ring 3 — Learning | System improves over time | Proposes changes, never autonomously enacts them |
Two additional structures complete the architecture:
- Cross-cutting Fabric — events, structured output, identity, provenance, error recovery, and security enforcement that operate across all rings
- Environment Substrate (#19) — governed context, instructions, tools, workspace, and memory that shape agent behavior before execution begins
19 Named Primitives
Not invented — named for the agentic context. Patterns drawn from distributed systems, security engineering, compliance, and control theory, organized into three categories:
17 runtime primitives (#1-#17) operate within the ring pipeline during execution. 1 lifecycle primitive (#18 Evaluation & Assurance) gates what enters production. 1 substrate primitive (#19 Agent Environment Governance) governs the operating environment itself.
Key primitives:
- Trust Ladders (#11) — agents earn autonomy through demonstrated performance, not configuration
- Governance Gates (#8) — execution pauses for human authorization at material decisions
- Policy as Code (#9) — governance rules as versioned, testable, deployable objects
- Provenance Chains (#6) — every output carries its full decision history
- Adversarial Robustness (#15) — assume breach, defense in depth
Deployment Modes
The Rings Model is a logical architecture. How the rings manifest physically depends on the system:
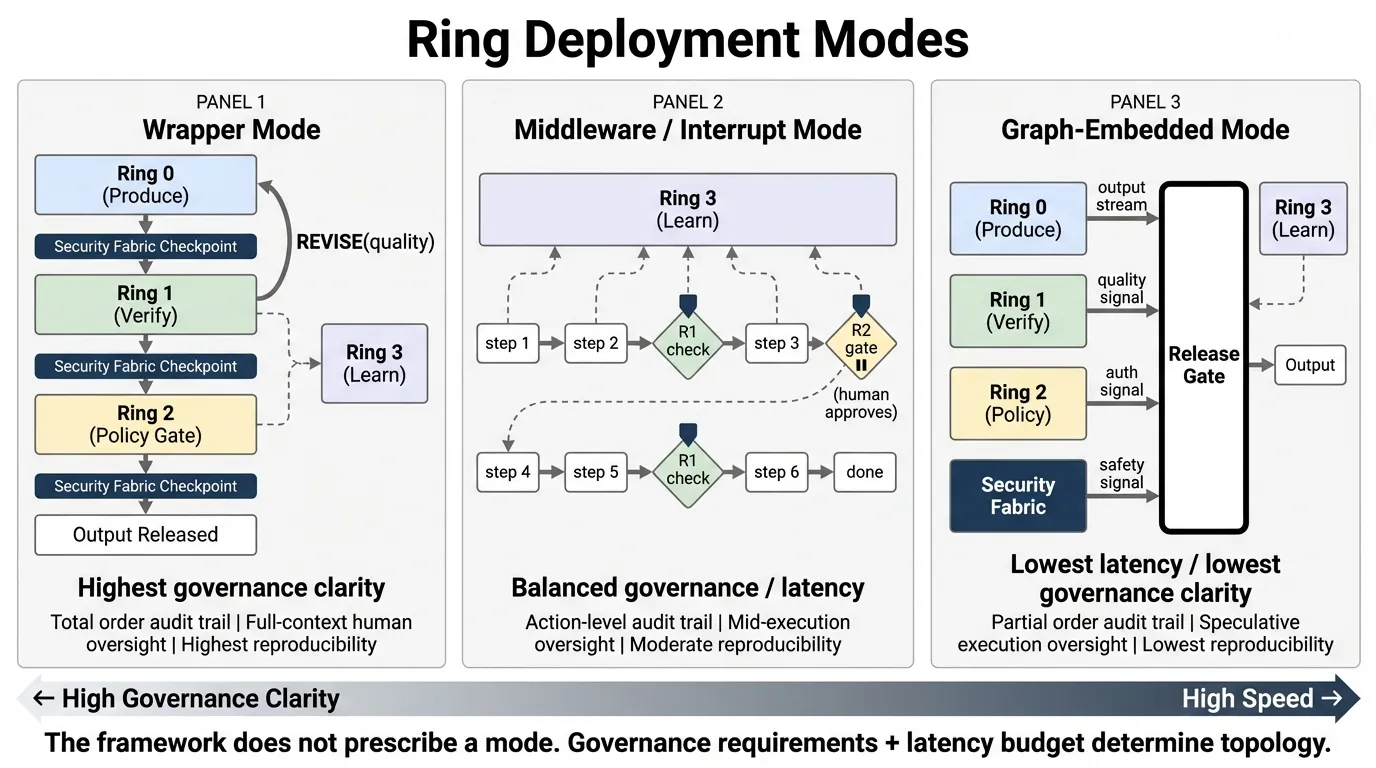
- Wrapper Mode — sequential rings wrapping execution (batch pipelines, regulatory assessments)
- Middleware / Interrupt Mode — ring logic at tool-call boundaries (coding agents, MCP)
- Graph-Embedded Mode — concurrent verification alongside execution (conversational agents)
Three-Level Security Model
Security is pervasive, not a single layer:
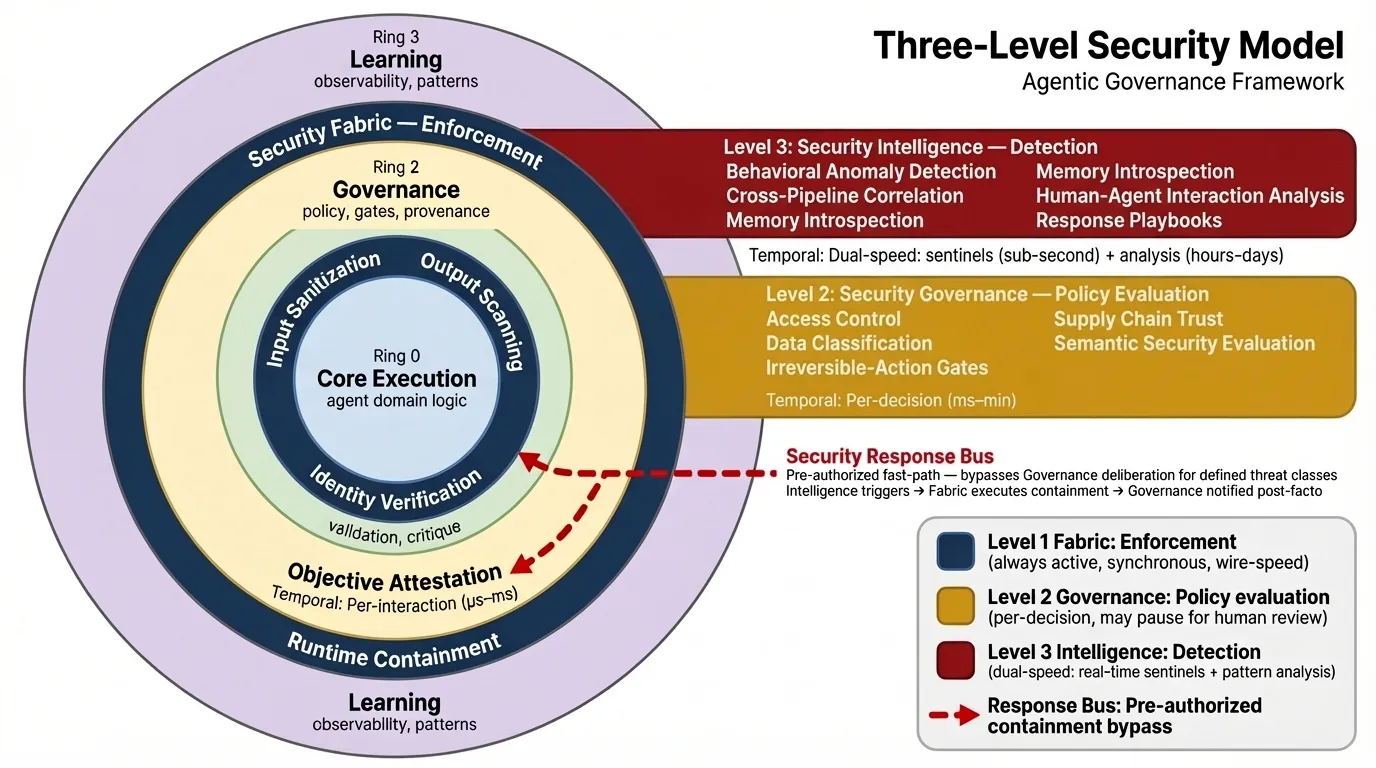
- Level 1: Security Fabric — enforcement at wire speed, always active
- Level 2: Security Governance — policy evaluation in Ring 2
- Level 3: Security Intelligence — detection, correlation, response (SIEM for agents)
- Security Response Bus — pre-authorized fast-path containment for attacks that cascade faster than governance deliberation
Composition Patterns
Organizations start simple and grow governance as stakes increase:
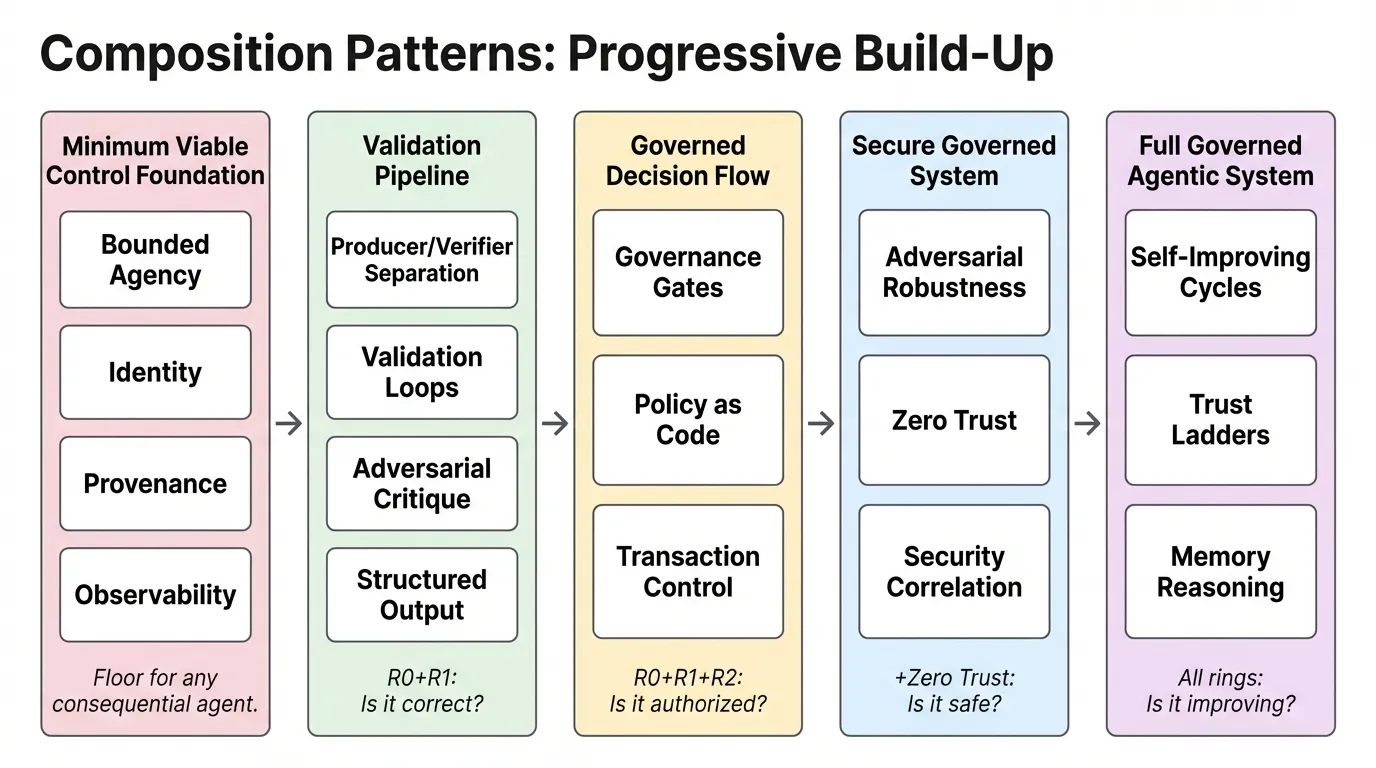
- Minimum Viable Control — scope, identity, audit trail (the floor)
- Validation Pipeline — verified outputs (Ring 0 + Ring 1)
- Governed Decision Flow — policy-evaluated, human-gateable decisions (+ Ring 2)
- Secure Governed System — defense in depth, pre-deployment validation (+ security)
- Full Governed Agentic System — everything, improving over time (all rings)
Domain Profiles
AGF serves five professional audiences, each with a dedicated profile:
| Audience | Profile | Focus |
|---|---|---|
| CISOs, security architects | Security | OWASP ASI/MCP threat mapping, MITRE ATLAS alignment, red team scenarios, incident response |
| Platform engineers | Platform | Deployment modes, mode selection matrix, MCP integration, cost of governance |
| Compliance officers, auditors | GRC | EU AI Act article mappings, NIST 800-53/ISO 27001 crosswalks, maturity model |
| AI engineers | AI Engineering | 19-primitive catalog, 5-phase implementation roadmap, composition patterns |
| SREs, detection engineers | Observability | Event architecture, correlation rules, dual-speed detection, OTel alignment |
Standards Alignment
| Standard | AGF Coverage |
|---|---|
| EU AI Act | Article-level mapping (Art. 6, 9-15, 50) with phased applicability |
| NIST AI RMF | AGF as an agentic AI RMF-style profile |
| OWASP ASI Top 10 | All 10 agentic threats mapped to defense architecture |
| OWASP MCP Top 10 | All 10 MCP threats mapped to primitives |
| CSA MAESTRO | 7-layer threat model mapped to primitives |
| MITRE ATLAS | Security architecture aligned to adversarial technique taxonomy |
| NIST 800-53 / ISO 27001 | Control crosswalks in GRC Profile |
| Singapore IMDA | 4-dimension mapping to AGF primitives |
| OpenTelemetry GenAI | Event architecture as OTel-compatible base + governance extensions |
Status
AGF is open source under CC BY 4.0. The full framework, all five domain profiles, and white papers are available at agf.jessepike.dev. Source is on GitHub.
The framework evolved from the earlier AFAS (Architecture Framework for Agentic Systems) after practice revealed that the governance challenge was broader than architecture alone. The writing on this site — posts on governance velocity, agentic identity, and the puzzle of sorting governance frameworks — are AGF ideas in applied form.
Outcome Signals
- Published Framework: Open-source reference architecture (CC BY 4.0) with 19 named primitives, five domain profiles, and standards crosswalks across 9+ frameworks.
- Standards Alignment: Article-level EU AI Act mapping, OWASP ASI/MCP threat coverage, NIST 800-53/ISO 27001 control crosswalks, MITRE ATLAS alignment.
- Practitioner-First: Five deployment profiles for security architects, platform engineers, compliance officers, AI engineers, and SREs.